February 8 - 14, 2015: Issue 201
Bought a new tablet for school? Some tips to Keep It and You Safe
Bought a new tablet for school? Some tips to Keep It and You Safe
Mobile Devices, Tablets etc.
Mobile devices like smartphones and tablets are basically small portable computers. Just like your computer at home they can be hacked, infected with a virus and, if unsecured, provide access to your personal information.
 Protect yourself and your mobile device
Protect yourself and your mobile device
Keep your mobile device with you at all times. Remember if your mobile device is unsecured and it is lost or stolen:
• it could be used to access your money or to steal your identity using information on your device
• you may have lost irreplaceable data (if it is not backed up)
• it may provide access to your social media accounts which could enable someone to pose as you, or steal your identity using your profile information (such as your date of birth and photo)
• someone may use your phone or its Subscriber Identity Module (SIM) card and rack up telephone charges to your account.
Remember your smartphone or tablet is a mini-computer and you need to protect and secure it just as you would you home or laptop computer. Treat your smartphone like your wallet; keep it safe and with you at all times.
Secure your mobile device
• Turn on the security features of your device – all devices have them. Contact your manufacturer or service provider for instructions, or look them up online.
• Set a password or Personal Identification Number (PIN) that must be entered to unlock the device and put PINs on your SIM card and voicemail.
• Install reputable security software – your device's manufacturer can provide recommendations.
• Update your device's operating system as soon as new updates are available. Set them to update automatically when connected to wi-fi to keep data costs to a minimum.
• Leave your Bluetooth turned off or in undiscoverable mode (hidden) when you are not using it. When connecting using Bluetooth, do it in private, uncrowded areas only.
• Use encrypted wi-fi networks that require a password and ensure your device does not automatically connect to new networks.
• Record the International Mobile Equipment Identifier (IMEI) of your handset, a 15 or 17 digit number usually printed on a label under the battery. If your device is lost or stolen, you can report this number to your provider and they can block the handset from being used.
• Use remote tracking (via GPS), enabling the locking and/or wiping functionality if your device supports it.
• Remember to clear your cache, or 'History' on a weekly or monthly basis - this prevents add-ons, cookies etc. and tracking of your activity
Secure your information
• Back up your data regularly, either when you synchronise it with a computer or on a memory card.
• Do not save passwords or PINs as contacts on your phone.
• Avoid online banking over public Wi-Fi or in busy public areas. Passers-by could be watching what you are typing (known as shoulder-surfing).
 Protecting personal information and privacy
Protecting personal information and privacy
You are recognised online by your personal details. If the wrong person has that information they can steal your identity, pretend to be you on social media and even access your finances.
Educate yourself on how to protect their personal information and privacy
Do not give out personal details about yourself or your family including:
full name, date of birth or age
where you live
where your children go to school
contact details including email addresses
bank account details
user names and passwords.
Help yourself understand the importance of using strong usernames and passwords that do not reveal anything personal. For example 'Katy1998' could reveal name, gender and age. Use a different username and password for each online account.
Recognise spam; usually messages from people or organisations you do not know, and delete them without opening them.
If you are not sure about whether you should be sharing something online, ask an adult first.
Encourage family discussions about safe online practises, making it easy for kids and teens to ask you anything.
Where to get help
Online safety information targeted for young people:
Cybersmart website - 1800 880 176
Easy Guide to Socialising Online
Report abuse or suspicious activity
Crimestoppers - 1800 333 000
Your local police station
Report offensive, illegal or prohibited content
Australian Communications and Media Authority
Using applications (apps) on mobile devices
Many apps have the ability to collect and transmit data from your device about your personal information, location, contacts and messages. You can control the personal information accessed by the apps by choosing permissions at the time of installation.
Be careful of downloading hoax or malicious software that could contain a virus or malware. Always source your apps from reputable providers and review the feedback other users leave. If you are unsure why an app needs access to your contacts, calls, photos or location, see if there is an alternative app available that has the same functionality that you require.
Be smart about how and where you use your mobile device
• Stick with reputable sites and applications when downloading anything from the internet.
• Do not download content, particularly applications, from unknown or unreliable sources. They could contain malicious software.
• Turn GPS settings off when not in use as this can be used to track your location.
• Log out of websites when you are finished.
• Think before you click. Do not open anything unless you are expecting it and it is from a trusted source. It could contain malicious software or take you to a malicious website.
• Change your settings so that your device asks permission to join any new wireless networks.
Protect against malicious software (malware)
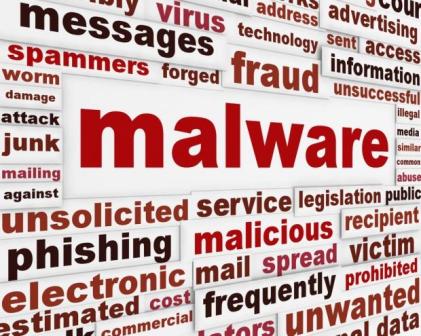 Viruses, spyware, trojans and worms are all types of malware. Malware is software designed to be installed into a computer system to cause harm to the user or others.
Viruses, spyware, trojans and worms are all types of malware. Malware is software designed to be installed into a computer system to cause harm to the user or others.
Malware can track your movements in the real world and steal information (including passwords) for the purposes of identity theft or crime.
• Watch out for prompts or warnings asking if you want to allow software to install or run. If you do not know what it is, do not accept the prompt.
• Avoid 'rooting' or 'jailbreaking' your device. Rooting or jailbreaking involves intentionally bypassing software restrictions in the device to enable additional flexibility or functionality, but it also bypasses security restrictions exposing your device to malware threats.
• Only use legitimate app stores: avoid 'side loading' from third party app stores, as these are more likely to harbour malware (even in seemingly legitimate apps).
• Check app permissions. When an app is installed it has to ask the user for 'permission' to use specific types of functionality. Consider whether you want that app to have access to your information.
• Keep a close watch on your billing information. Some malware makes money for scammers by sending SMSs from your device to premium-rate numbers. Contact your carrier immediately if you see any unexpected activity on your account.
Symptoms of malicious software infections
Your device may have been infected with malicious software if any of the following things have happened:
• There is a sudden increase in your phone or data bill with no clear reason.
• Your device has emails and messages in the sent folder that you did not send.
• The user interface changed without you taking any action to change it.
Contact your service provider for instructions on how to identify and remove malicious software.
Using public wireless networks
Public wi-fi 'hotspots' in public places like cafés, airports, hotels and libraries are convenient but unlike your home computer, use of public hotspots involves security compromises. It is easy for other users to intercept your data, so be careful about what information you send or receive while connected. Try and limit activity when connected to a public wi-fi network to web browsing and avoid banking or any other activities that involve user password access.
Avoid using hotspots that are run by people you do not know or trust. Criminals can set up hotspots known as 'evil twins' and 'rogue hotspots' to steal users' information.
Always try and use encrypted (password protected) networks.
Choose networks with WPA2 and WPA encryption if they are available as they are more secure than other types of security encryption.
Connect using the right network type
When you connect to a wi-fi network many devices will prompt you to select or identify the network type ('home', 'work' or 'pubic'). Always select 'public' when you connect to a public wi-fi network as this will lock down the connection more securely.
Use a virtual private network (VPN) if possible as they encrypt connections at the sending and receiving ends and keep out traffic that is not properly encrypted.
If you can not connect securely using a VPN, avoid:
• online banking or shopping
• sending confidential emails
• entering passwords or credit card details unless using a secure website
• using passwords, credit card details, emails, online documents or social networking.
If making sensitive transactions, only use secure websites and look for:
• https:// instead of http://
• a locked padlock or key in the browser website address bar.
Courtesy Stay Smart Online - keep up to date here: www.staysmartonline.gov.au/home
Brief History of the Internet
By Barry M. Leiner, Vinton G. Cerf, David D. Clark, Robert E. Kahn, Leonard Kleinrock, Daniel C. Lynch, Jon Postel, Larry G. Roberts, Stephen Wolff
Introduction
The Internet has revolutionized the computer and communications world like nothing before. The invention of the telegraph, telephone, radio, and computer set the stage for this unprecedented integration of capabilities. The Internet is at once a world-wide broadcasting capability, a mechanism for information dissemination, and a medium for collaboration and interaction between individuals and their computers without regard for geographic location. The Internet represents one of the most successful examples of the benefits of sustained investment and commitment to research and development of information infrastructure. Beginning with the early research in packet switching, the government, industry and academia have been partners in evolving and deploying this exciting new technology. Today, terms like "bleiner@computer.org" and "http://www.acm.org" trip lightly off the tongue of the random person on the street.
This is intended to be a brief, necessarily cursory and incomplete history. Much material currently exists about the Internet, covering history, technology, and usage. A trip to almost any bookstore will find shelves of material written about the Internet.
In this paper, several of us involved in the development and evolution of the Internet share our views of its origins and history. This history revolves around four distinct aspects. There is the technological evolution that began with early research on packet switching and the ARPANET (and related technologies), and where current research continues to expand the horizons of the infrastructure along several dimensions, such as scale, performance, and higher-level functionality. There is the operations and management aspect of a global and complex operational infrastructure. There is the social aspect, which resulted in a broad community of Internauts working together to create and evolve the technology. And there is the commercialization aspect, resulting in an extremely effective transition of research results into a broadly deployed and available information infrastructure.
The Internet today is a widespread information infrastructure, the initial prototype of what is often called the National (or Global or Galactic) Information Infrastructure. Its history is complex and involves many aspects - technological, organizational, and community. And its influence reaches not only to the technical fields of computer communications but throughout society as we move toward increasing use of online tools to accomplish electronic commerce, information acquisition, and community operations.
Whole paper/Article at: www.internetsociety.org/internet/what-internet/history-internet/brief-history-internet
Also:
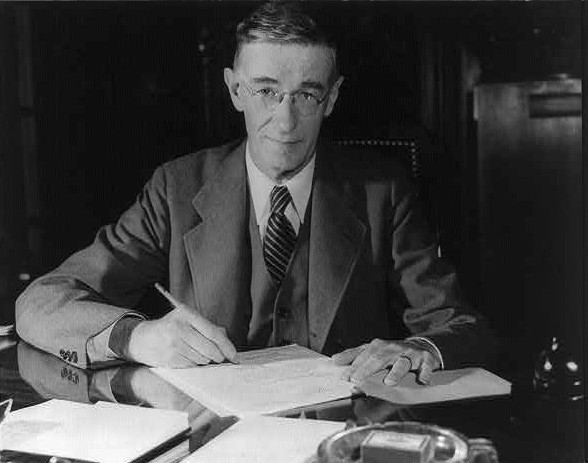 Vannevar Bush (March 11, 1890 – June 28, 1974) was an American engineer, inventor and science administrator, whose most important contribution was as head of the U.S. Office of Scientific Research and Development (OSRD) during World War II, through which almost all wartime military R&D was carried out, including initiation and early administration of the Manhattan Project. He is also known in engineering for his work on analog computers, for founding Raytheon, and for the memex, an adjustable microfilm viewer with a structure analogous to that of the World Wide Web.
Vannevar Bush (March 11, 1890 – June 28, 1974) was an American engineer, inventor and science administrator, whose most important contribution was as head of the U.S. Office of Scientific Research and Development (OSRD) during World War II, through which almost all wartime military R&D was carried out, including initiation and early administration of the Manhattan Project. He is also known in engineering for his work on analog computers, for founding Raytheon, and for the memex, an adjustable microfilm viewer with a structure analogous to that of the World Wide Web.
In 1945, Bush published As We May Think in which he predicted that "wholly new forms of encyclopedias will appear, ready made with a mesh of associative trails running through them, ready to be dropped into the memex and there amplified". The memex influenced generations of computer scientists, who drew inspiration from its vision of the future.
As We May Think presented Bush's conception of the Memex, a machine that could implement what we now call hypertext, believing that such an invention could give humanity the capability of a collective memory, his aim being to enable humanity use this collective knowledge to achieve the wisdom necessary to avoid exploiting scientific discoveries for destruction and war. Today, all Internet-connected people of the planet can access a huge portion of the world's knowledge through websites on the World Wide Web through such a concept realised.
As We May Think predicted (to some extent) many kinds of technology invented after its publication, including hypertext, personal computers, the Internet, the World Wide Web, speech recognition, and online encyclopedias such as Wikipedia: "Wholly new forms of encyclopedias will appear, ready-made with a mesh of associative trails running through them, ready to be dropped into the memex and there amplified."
Right: Vannevar Bush seated at a desk. This portrait is credited to "OEM Defense", the Office for Emergency Management (part of the United States Federal Government) during World War II; it was probably taken some time between 1940 and 1944.
As We May Think. (2015, January 5). In Wikipedia, The Free Encyclopedia. Retrieved from http://en.wikipedia.org/w/index.php?title=As_We_May_Think&oldid=641145820